Introducing ActiveLogin
Intro

ActiveLogin is an open source package that I created together with a few colleagues back in 2018 and published on github in 2019. With the purpose of simplifying the authentication process with BankID-services. Current version is 3.0.0
I will quote the main description from our https://activelogin.net website:
What is Active Login?
Active Login is an Open Source project built on .NET Standard that makes it easy to integrate with leading Swedish authentication services like BankID.
The package also provides examples on how to use it with the popular OpenID Connect & OAuth 2.0 Framework IdentityServer and provides a template for hosting the solution in Microsoft Azure. In addition, Active Login contains convenient modules that help you work with and handle validation of Swedish Personal Identity Number.
Lead
BankID has become a default tool to be logged-in to many web sites, mobile applications and especially important for the bank sector.

You can even use BankID to sign important documents or transactions. You can see it almost everywhere nowadays in IT life in Sweden, but what if you want to integrate a BankID service by yourself? Usually this integration is a bit of a struggle.
If we take a brief look at the historical timeline, we will see that early on there were some endpoints to communicate with BankID via SOAP/XML. Then in February 2018, there was a really big release - a new endpoint: v5, - working above Http/JSON, REST!
But then comes the question: How to work with this endpoint? Of course there is the technical documentation, but it is BIG…
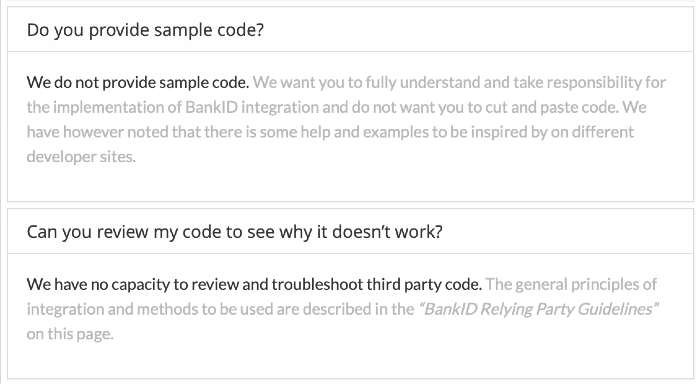
And even more so in the BankID FAQ they explicitly say that they won’t help you with your code, so we end up in a situation where there are no samples or personal help.
Idea
To be honest, authentication by itself is a bit of a hassle, there are so many standards and implementations to consider. But thanks to smart people, many of these challenges have already been solved.
For example, we can install some nuget packages (like IdentityServer) write two-three lines of configuration code (like services.AddIdentityService with some arguments), and you are ready to go…
People who work with authentication know that if you want to use a custom authentication - you need to work with the custom AuthenticationHandler. But in our case with BankID as a third party identity provider, Microsoft documentation says that we need to use RemoteAuthenticationHandler.
So how do we do this? - Ehm funny fact, in Microsoft’s documentation it does not show how.
Microsoft security specialist in .Net area explicitly says that you should not implement your custom authentication handler until you really know what you are doing. And in most cases it is not even necessary, because Microsoft already have many built in authentications that cover most mainstream cases.
But when it comes to BankID - which is very local for Sweden - the situation is very different as Microsoft does not provide an out-of-the-box solution.
We, at ActiveSolution, faced the same problems as other developers before us when working with BankID, we could not find documentation or proper examples to easily implement a custom authentication handler.
Thanks to the new Microsoft strategy - where they put a lot of code to open source - we found how Microsoft implemented a RemoteAuthenticationHandler for Twitter.
Looking into the Twitter authentication project we got inspired to create a simplified open source solution for BankID, and that is how we came up with the idea to create Active Login.
Links
On our github repo https://github.com/ActiveLogin/ActiveLogin.Authentication you can find very detailed documentation and samples.
Here are the nuget package that might be useful for you:
| Project | Description | NuGet | Downloads |
|---|---|---|---|
| BankId.Api | API client for the Swedish BankID REST API. |  |
 |
| BankId.AspNetCore | ASP.NET Core authentication module for Swedish BankID. |  |
 |
| BankId.AspNetCore.Azure | Azure integrations for the AspNetCore package. |  |
 |
| BankId.AspNetCore.QRCoder | QR code generation using QRCoder the AspNetCore package. |  |
 |
You can also try our live demo website to see full power of the package:
| Live demo | Project | Description |
|---|---|---|
| https://al-samples-mvcclient.azurewebsites.net | IdentityServer.ClientSample | ASP.NET MVC Core site using the IdentityServer.ServerSample as auth provider. |
| https://al-samples-identityserver.azurewebsites.net | IdentityServer.ServerSample | IdentityServer with Active Login as auth provider for BankID and GrandID. |
Please note that IdentityServer.ClientSample uses IdentityServer.ServerSample as the IdentityProvider, so the IdentityServer.ClientSample is a good place to start.
Identity
During the development process we faced with a problem of parsing and validating swedish personal identity number. As an addition to our BankID project we ended up creating a separate package ActiveLogin.Identity which provides parsing and validation of Swedish identities such as Personal Identity Number (svenskt personnummer) and Coordination Number (samordningsnummer):
| Project | Description | NuGet | Downloads |
|---|---|---|---|
| ActiveLogin.Identity.Swedish | .NET classes handling Personal Identity Number |  |
 |
| ActiveLogin.Identity.Swedish.AspNetCore | Validation attributes for ASP.NET Core. |  |
 |
| ActiveLogin.Identity.Swedish.TestData | Provides Swedish Identity Numbers test data. |  |
 |
Summary
We spent hundreds of hours on this product and learned a lot, and to sum it up I would like to emphasize some key points:
- We implemented this package based on the best practices on how to work with secure flow, like OpenId;
- Certificate handling, we have a default support for storing Azure certificate;
- Our solution supports working with BankID directly or via Svensk E-Identitet (GrandID);
- BankID demands a special format of SPIN, 12 characters (YYYYMMDDNNNN), but we allow several different forms, like with delimiter or without;
- Component based development. If you are not a big bank company - why not use an open source package;
- We are proud that we use as few 3rd party depencencies as possible. At the moment we only use one external library if the customer chooses to use QR codes;
- The concept of open source - we value the OpenSource community and as part of that we work with pull requests, and have open discussions on improvements. Plus, OpenSource provides us the possibility to be transparent which is key when working on security matters like authentication.